Cybersecurity has become an increasingly critical concern for mobile users, especially with the rise of sophisticated malware. Recently, researchers uncovered a new Android banking Trojan known as Crocodilus. This threat, primarily targeting users in Spain and Turkey, showcases advanced capabilities that differentiate it from typical malware.
What is Crocodilus?
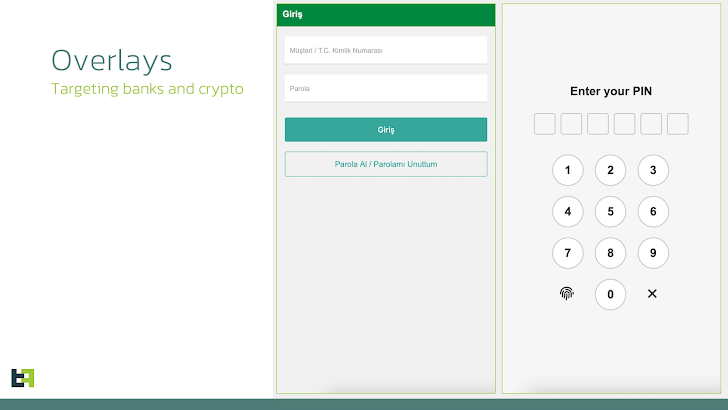
Crocodilus is not just another malware clone; it presents a fully-fledged threat from its inception. According to ThreatFabric, this Trojan utilizes modern techniques such as remote control functionalities, black screen overlays, and advanced data harvesting via accessibility logging.
How Does Crocodilus operate?
This Android Trojan operates by masquerading as a legitimate application, sporting the package name “quizzical.washbowl.calamity” which imitates Google Chrome. Once installed, it requests permissions to access Android’s accessibility services. This is crucial, as it allows the malware to establish a connection with remote servers, enabling it to receive instructions on targeted financial applications and HTML overlays for credential theft.
Targeting Banking and Cryptocurrency Apps
One of Crocodilus’ distinguishing features is its ability to target cryptocurrency wallets. Instead of traditional phishing tactics like fake login screens, it employs a social engineering trick by presenting a message encouraging victims to secure their seed phrases. This is a clever ruse to direct users to display their sensitive information, which the malware then harvests through accessibility services.
Key Features of Crocodilus
The Growing Threat of Sophisticated Malware
The emergence of Crocodilus underscores a significant escalation in the sophistication of threats facing mobile users. With advanced device takeover capabilities and the deployment of black overlay attacks, Crocodilus demonstrates an alarming maturity in newly discovered malware.
According to cybersecurity experts, the continuous monitoring features and stealthy operations of Crocodilus make it a formidable risk for unsuspecting users. As the Trojan remains active, it monitors app launches, displaying overlays to intercept credentials without the victim’s awareness.
Conclusion
As the digital landscape continues to evolve, staying informed about the latest threats is crucial. The Crocodilus Trojan is a clear reminder of the importance of maintaining vigilant cybersecurity practices, particularly for those using banking and cryptocurrency applications on Android devices.
For mobile users, ensure your devices are equipped with robust security measures and remain aware of potential threats that could disrupt your financial security. Follow our blog for more insights into the latest cybersecurity trends and threats!
